Remote access solutions could leave you vulnerable. If you don’t have proper security solutions in place, remote connections could act as a gateway for cybercriminals to access your devices and data. Hackers could use remote desktop protocol (RDP) to remotely access Windows computers in particular.
What happens when a hacker get remote access to my computer?
Hackers use RDP to gain access to the host computer or network and then install ransomware on the system. Once installed, regular users lose access to their devices, data, and the larger network until payment is made.
Can someone remotely access my computer without my knowledge?
There are two ways someone can access your computer without your consent. Either a family member or work college is physically logging in to your computer or phone when you are not around, or someone is accessing your computer remotely.
What can a scammer do with remote access to your computer?
In a remote access scam, a scammer attempts to persuade you into giving them remote control over your personal computer, which allows the scammer to con money out of you and steal your private information.
Can someone remotely access my computer without my knowledge?
There are two ways someone can access your computer without your consent. Either a family member or work college is physically logging in to your computer or phone when you are not around, or someone is accessing your computer remotely.
What can a scammer do with remote access to your computer?
In a remote access scam, a scammer attempts to persuade you into giving them remote control over your personal computer, which allows the scammer to con money out of you and steal your private information.
Does shutting down computer stop hackers?
In general, the answer is no, you cannot hack into a computer that’s been turned off. Unless two conditions are met, the PC cannot be restarted and hacked from outside, even if you leave it connected to the internet and to power.
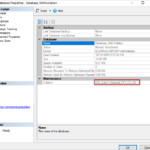
How do I see who is connected to my computer?
right click on my computer -> manage ->shared folders -> sessions/open files. that will tell you what windows shares they are looking at.
What happens if you give a scammer access to your phone?
By having your cell number, a scammer could trick caller ID systems and get into your financial accounts or call financial institutions that use your phone number to identify you. Once the scammer convinces your carrier to port out your number, you may never get it back. Scam porting is a big problem for phone owners.
Can a scammer access my bank account?
How do I remove computer name from remote desktop?
Remove entries in the Windows Remote Desktop Connection client. Entries appear as MRUnumber, and are visible in the right pane. To delete an entry, right-click it, and then select Delete.
What can a scammer do with AnyDesk?
AnyDesk is used legitimately by millions of IT professionals worldwide, to remotely connect to their clients’ devices to help with technical issues. However, scammers can try to misuse AnyDesk (or any other remote access software) to connect to your computer and steal data, access codes, and even money.
What is UltraViewer used for?
UltraViewer is a software that help you to remote control/remote access a computer. You can use UltraViewer for many difference purpose : to support your customers, your partners, your friends, or access your computer to work remotely…
Can someone remotely access my computer without my knowledge?
There are two ways someone can access your computer without your consent. Either a family member or work college is physically logging in to your computer or phone when you are not around, or someone is accessing your computer remotely.
What can a scammer do with remote access to your computer?
In a remote access scam, a scammer attempts to persuade you into giving them remote control over your personal computer, which allows the scammer to con money out of you and steal your private information.
How would you know if your computer has been hacked?
Frequent pop-up windows, especially the ones that encourage you to visit unusual sites, or download antivirus or other software. Changes to your home page. Mass emails being sent from your email account. Frequent crashes or unusually slow computer performance.
Can WIFI be hacked remotely?
You might be surprised how easy it is to hack into your home Wi‑Fi network nowadays. For very little money, a hacker can rent a cloud computer and most often guess your network’s password in minutes by brute force or using the powerful computer to try many combinations of your password.
How do hackers take over your computer?
Another common way that hackers use to gain control of your computers is by sending out Trojan Viruses disguised as email attachments. Hackers typically send out these messages to 1000s of users with enticing headings and an attachment which they are hoping you will open.
Can hackers access a sleeping computer?
A computer cannot be hacked “in” sleep mode, but it can be hacked either if the user resumes his or her computer to make it back into functioning under the power of the operating system or the hacker triggers a Wake-on-Lan (WOL).
Open task manager by right-clicking on the taskbar and choosing Task Manager. If there’s a suspicious process, that’s the monitoring app. Question: Can my company see what I do on my computer? Answer: Your company can see your device activities and track them if they provide you with that computer.
What do I dial to see if my phone has been hacked?
Use the code *#21# to see if hackers track your phone with malicious intent. You can also use this code to verify if your calls, messages, or other data are being diverted. It also shows your diverted information’s status and the number to which the information is transferred.prieš 4 dienas
What’s the worst someone can do with your phone number?
If someone steals your phone number, they become you — for all intents and purposes. With your phone number, a hacker can start hijacking your accounts one by one by having a password reset sent to your phone. They can trick automated systems — like your bank — into thinking they’re you when you call customer service.
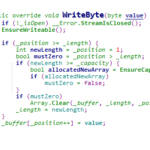
What happens when a technician remotely accesses your computer?
When a technician is remotely accessing your computer, you may be able to see what they are doing. Often, remote access software will show the other person’s actions to you on the screen. In addition to being able to see, there may be some kind of communication between you and the technician.
What is remote computer access and how does it work?
Remote computer access allows an employee to access a computer desktop and its files from a remote location. This helps enable an employee who is working from home, for instance, to work effectively.
How can a person gain remote access to my computer?
There are several ways a person can gain remote access. 1. The user downloads a virus through a file or pic of an unknown sender. 2. Through remote assistance ( this has to be verified by the owner of the computer first. I would advise you to never give out personal information to someone they don’t know especially over the phone.
Is it safe to give someone remote access to your computer?
You may get a phone call from someone asking to get access to your computer so that they could carry out essential work to protect your computer. But, is it safe to give someone remote access to your computer? Allowing someone to remotely access your computer is not a bad thing, it can be very helpful.